-
How to resolve “This app has been blocked for your protection”
“This app has been blocked for your protection” tends to show up at the worst time, right when you’re trying to open or install an app you trust. The tricky part is that Windows uses similar lan...
-
ECDSA vs. RSA: Security, compatibility, and key size compared
Rivest-Shamir-Adleman (RSA) and Elliptic Curve Digital Signature Algorithm (ECDSA) underpin everyday security, including website authentication, app login verification, and software updates verified b...
-
How to disable WebRTC and stop IP leaks in major browsers
You turn on your virtual private network (VPN), open your browser, and your IP address should be private. It isn’t always. WebRTC, a technology built into every major browser for real-time audio, vi...
-
Token-based authentication explained: How it works, benefits, and best practices
Many modern apps let you refresh a page without having to re-enter your password, stay logged in across sessions, or use one account to access multiple services. This is made possible by token-based a...
-
What is DNS over HTTPS (DoH) and how does it work?
DNS over HTTPS (DoH) sends Domain Name System (DNS) queries using HTTPS, the secure web protocol also used for encrypted website connections. That helps protect DNS traffic from being read or altered ...
-
Augmented reality vs. virtual reality: What’s the difference and why does it matter?
Augmented reality (AR) and virtual reality (VR) are often grouped together, but they offer very different experiences and are used in different ways. AR adds digital elements to your surroundings, whi...
-
Tracking pixel: How it works and how to protect your privacy
Tracking pixels are small, hidden tools that help companies measure what people do online. They can log signals such as email opens, page visits, ad clicks, and conversions, often without any obvious ...
-
Third-party vs. first-party cookies: What’s the difference and why does it matter?
First and third-party cookies are different ways websites store and access data in your web browser. First-party cookies are set and used by the website you visit, while third-party cookies come from ...
-
Digital safety resources every activist should know about
Activists face a growing mix of digital and physical threats. Targeted surveillance and spyware, doxxing and harassment, phishing and account takeovers, platform censorship, and even device loss or th...
-
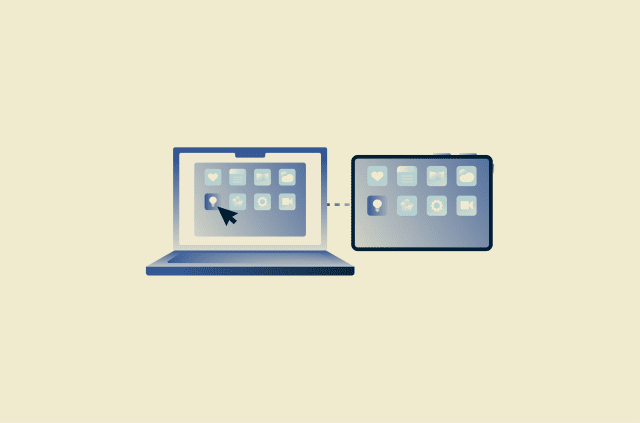
How to control an iPad remotely from iPhones and Macs
If you need to access or control your iPad without using it directly, the available options can vary widely depending on your setup and what you’re trying to do. Apple includes several features that...
-
- No-Logs Policy
- Servers in 105 Countries
- Use on Multiple Devices
- High-Speed VPN
- Access Online Services Securely
- VPN for Gaming
- 30-Day Money-Back Guarantee
- Explore All Features
- About ExpressVPN
One subscription gives you access to a fast-growing suite of privacy and security tools that work seamlessly together to improve your digital life.
View all products - Download VPN
- Pricing
- VPN for Teams
- Products
-
ExpressVPN Industry-leading, ultra-fast VPN with secure servers in 105 countries.
-
ExpressMailGuard Private email relay service to protect your inbox and identity.
-
ExpressKeys Secure password management, multi-factor authentication, and more.
-
ExpressAI The first consumer AI powered by confidential computing for privacy-led intelligence.
-
Identity Defender Powerful suite of ID protection, monitoring, and data removal tools
Other products from the family behind ExpressVPN
-
- My Account


